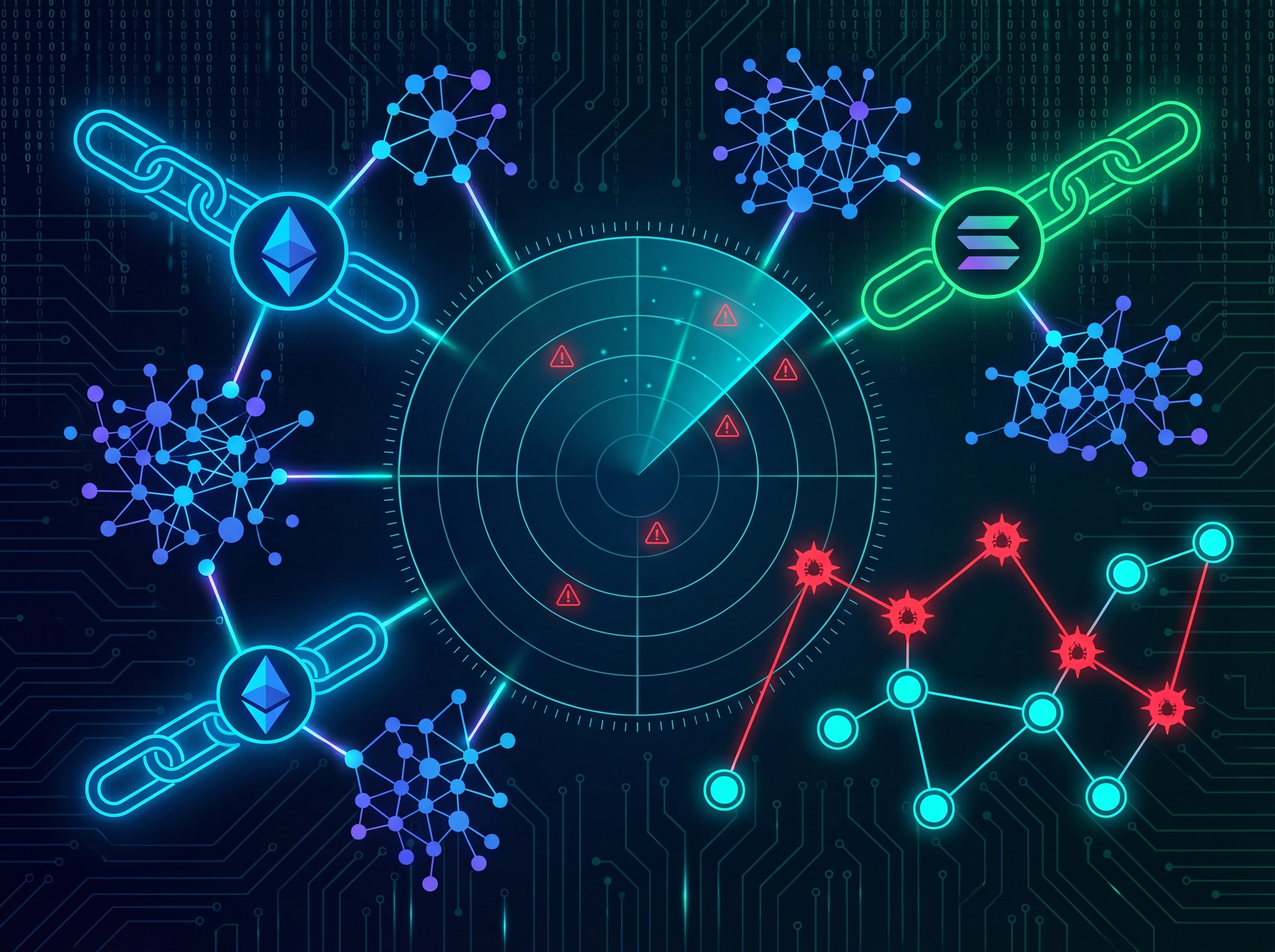
Cross-Chain Attack Path Visualizer
Interactive D3.js graphs map multi-contract attack vectors across EVM and Solana chains. Reveals complex exploit chains — flash loans, reentrancy cascades, oracle manipulation — that single-contract analyzers cannot detect.
- ✓ Interactive D3.js force-directed attack graphs
- ✓ Cross-contract call chain analysis
- ✓ Flash loan and oracle manipulation detection
- ✓ Exportable HTML reports with embedded visualizations